













Attackers may try to bypass verification using altered IDs or injected capture content. NFINITY helps detect common fraud patterns and improves the security and quality of the verification flow.
Presentation Attacks happen when an ID is shown to the camera. Attackers may use tampered documents or substitutes to pass as someone else. NFINITY’s Presentation Attack Detection (PAD) helps detect these attempts.
Enhanced for Slovak & Czech IDs to reduce false alarms, with optional fine-tuning.
Detects printed copies used in place
of an original ID document.
Detects altered, covered, or replaced portrait photos on physical documents.
Injection Attacks target the selfie step and the data stream. Instead of a live camera feed, attackers may inject manipulated frames (e.g., recordings, virtual cameras, or synthetic content). NFINITY’s Injection Attack Detection (IAD) helps detect these attempts during selfie capture.
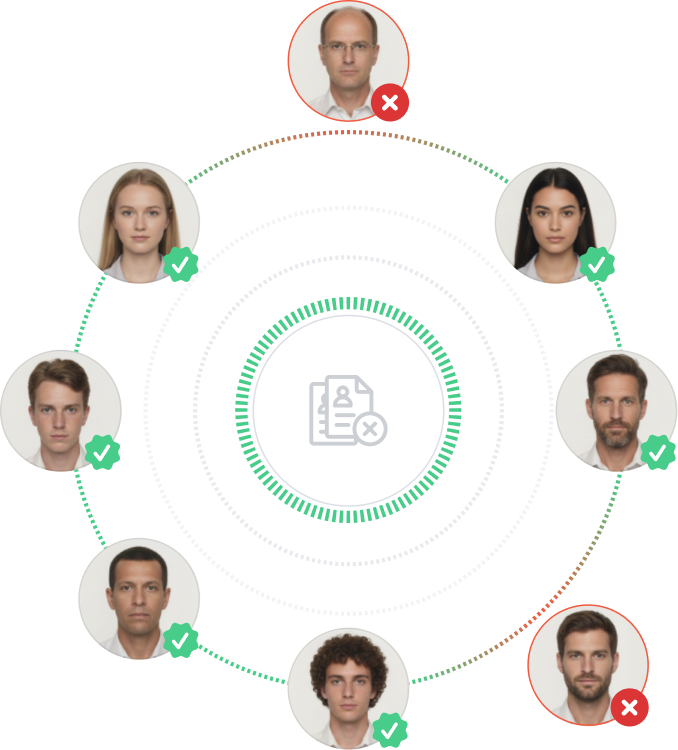
Block verification by matching an identity against a blacklist. Use manual lists or automate additions based on your rules.
By blocking known risky identities before verification completes
Manage a manual blacklist and automate additions based on your rules.
Set it as blocking (critical) or informational based on your risk policy.